Nowadays, it is impossible to overstate the importance of information technology in our daily lives. For corporations and organizations, it has made work a whole lot simpler, quicker, and more precise. After COVID, this took on a greater significance since the effectiveness of the online environment was further demonstrated during the lockdown. Unfortunately, this has also created opportunities for hackers to exploit, particularly if the proper security measures and precautions are not taken.
Since there is obviously a lot at stake, for non-profit firms tend to be more attentive of cybersecurity and security in general. Even though it might not seem like it at first, there is actually a lot to be done when it comes to non-profits. As a result, most non-profits tend to have insufficient cybersecurity, making them particularly vulnerable to attacks. According to studies, 50% of non-profit organizations have been the target of cyberattacks. Unfortunately, given the population’s rising tech proficiency, more may be to be expected in the near future.
Cyberattacks against non-profits can take many different forms. From modest probes that prepare a network for hacking and look for security gaps to more sophisticated threats like phishing, hacking, ransomware, malware, and so on. Non-profits are at a higher risk because they frequently act without thinking and, as a result, do not have the proper preventive or protective measures in place. Additionally, many non-profits operate in a way that allows staff to easily share access to networks, a practice that cybercriminals can exploit. Another issue is that cybersecurity typically receives insufficient funding, which means that cutting-edge security measures might not be in place.
As earlier mentioned, cybersecurity attacks on non-profit organizations are very detrimental, often because the right security checks may not be in place. Over and above this, the volume of sensitive information in their care is enormous. Information about donors, including their contact information, emails, addresses, mailing lists, meeting records, donation forms, research surveys, and so much more, could be exposed should there be a security breach. Of course, in addition to the financial implications, there may also be issues of trust and skepticism working with the organization going forward.
What, then, can be done? The truth is that these cybersecurity threats most likely would continue to exist. Doing a risk assessment, as advised by the Non-Profit Technology Network (NTEN), would help the non-profit see, more clearly, the need to be more cybersecurity conscious. How, then, can they protect their valuable and sensitive information and prevent them from getting into the hands of greedy and malicious cybercriminals?
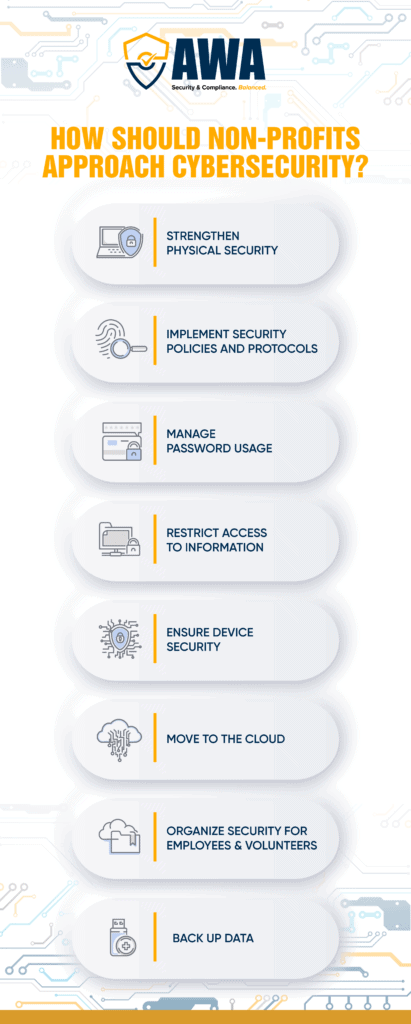
Below are some tips on how non-profits can better protect themselves from cyberattacks:
STRENGTHEN PHYSICAL SECURITY
Sometimes, destructive cyberattacks could result from some security details that were overlooked. It may not necessarily be that an armed cybercriminal came to the office and demanded the passwords to all the computers. But, if the password was opened and left unprotected for all to see on a computer, it could pose as a threat. An average office is comfortable, but that should not prevent an employee from taking the necessary security precautions to protect all passwords.
Also, with a lot of people working from home nowadays, it is vital to ensure that your workspace is secure, and that the minutest security detail is not overlooked. This culture should also be drummed into the ears of interns or new employees.
IMPLEMENT SECURITY POLICIES AND PROTOCOLS
Detailed security policies should be set up. Of course, these would contain plans for cyberattacks and what interventions would be implemented should they occur. It is advisable to have an IT person or team in the organization to attend to any cyber-related threats or suspicious-looking emails. External firms could also be employed to come in and make regular security checks.
MANAGE PASSWORD USAGE
In addition to ensuring that passwords are not shared carelessly, it may also be necessary to change them regularly or guarantee that they are “strong enough” before using them. Multi-factor authentication is also critical, as the user must supply the password and send another code. Google Authenticator could even be used to ensure more safety. Things have been made even easier with apps that could help encrypt and securely store passwords, making them safer for sharing in the workspace.
RESTRICT ACCESS TO INFORMATION
Access to certain sensitive information should be by necessity. Employees should have access to certain information only if their role in the non-profit demands it. This way, it is a lot easier to manage information. Of course, these restrictions could be changed after some time or by changing job descriptions. Proper documentation of all this should also be in place.
ENSURE DEVICE SECURITY
Computers, smartphones, and other devices should all be protected from cyberattacks. Keep in mind that these assaults take use of the existing weaknesses. As a result, every device needs to have antivirus, malware, and firewall software that is frequently updated. When sharing sensitive information, encrypted messaging applications should be utilized, and suspicious or unknown USBs should not be used. Also, phone software should be updated regularly, suspicious emails should be reported to the tech team, and staff members should be trained to recognize and respond to cyberattacks.
MOVE TO THE CLOUD
Cloud-based technology allows sensitive information to be stored safely and more securely. This is so because they encrypt the data, conduct regular data backups, and usually require multi-factor authentication before logins. That way, threats can be more easily be detected. Cloud-based accounting software, among others, is generally recommended.
ORGANIZE SECURITY FOR EMPLOYEES AND VOLUNTEERS
Security threats are often overlooked, not because the employees want the damage done to the organization, but because they are not aware that they are threats. It has been discovered that about 60% of non-profits do not provide security training for their employees. If employees and volunteers are informed and trained often on how to identify cyberattacks, usually in the form of phishing scams, the incidence of cyberattacks would drastically reduce.
BACK UP DATA
The importance of backing up essential data cannot be over-emphasized. Even if all the security checks are in place, it is wise to have an adequate backup for sensitive and vital data. The backups could be onsite or offsite. However, it is always safer to back up data using the cloud.
HOW SHOULD NON-PROFITS APPROACH CYBERSECURITY?
Non-profit organizations carry out important work and frequently handle sensitive data. Without confidence, there can be no business; hence it is crucial to handle sensitive data with the utmost caution. Putting procedures in place to block or thwart such attacks in any situation is one method to defend your organization as the number of cyberattacks rises daily. Non-profits are often unaware of this need, but this should change as cybersecurity becomes more prevalent.







