“Help! I need to perform a Cybersecurity Risk Assessment but have no idea where to start.”
I’ve heard this countless times by different organizations. Most have trouble determining where to start or what methodology to follow. For some, it makes sense to follow the NIST Risk Management Framework (RMF).
However, organizations with an international presence should also consider following Risk Management guidelines established by the International Organization for Standardization (ISO). While the NIST RMF provides a comprehensive process to manage information security and privacy risks centered around NIST standards and guidelines, NIST generally focuses on guidelines established by the United States. ISO on the other hand is an independent, non-governmental international organization with membership from 167 national standards bodies. ISO brings together experts to share knowledge and develop voluntary, consensus-based, market-relevant International Standards.
Of these standards, ISO/IEC 27001 includes requirements for establishing, implementing, maintaining, and continually improving an organization’s information security management system (ISMS). But before diving into ISO 27001 and the associated risk management/risk assessment process, it is important to understand a few benefits of pursuing the ISO/IEC 27001 certification.
- Competitive Edge – You are able to show outside organizations and potential customers how mature your security posture is especially when it comes to protecting sensitive assets such as financial information, intellectual property, PII, etc.
- Comprehensive Security Program – Obtaining the ISO 27001 certification helps provide better protection against emerging security threats. In order to become certified, you must prove that the necessary tools are in place to prevent, detect, and respond to both internal and external threats.
- Strong Risk Management and Cybersecurity Risk Awareness – ISO 27001 ensures that risk is assessed across your organization to ensure that your ISMS is protected from threats, vulnerabilities, and malicious actors.
ISO 27001 is broken down into various “Clauses” which are the information security requirements which organizations MUST adhere to. One of the most important clauses is Clause 6.1 which states, “Actions to address risks and opportunities.” Clause 6.1 contains multiple sub-requirements including the requirement for organizations to define and apply an information security risk assessment process that:
- “Establishes and maintains information security risk criteria
- Ensures that repeated information security risk assessments produce consistent, valid, and comparable results
- Identifies the information security risks
- Analyses the information security risks
- Evaluated the information security risks.”
Each organization must prove that risk assessments are performed periodically and focus on the organization’s ISMS. Even if your organization is not pursuing the ISO/IEC 27001 certification, it is still extremely important to identify, analyze, and evaluate information security risks presented to your organization.
You may be asking yourself; how should I go about performing a risk assessment which checks all the boxes that ISO requires? Well, there are 5 key steps which should be followed for performing a cybersecurity risk assessment focused on ISO 27001.
- Step 1: Determine Scope
- If you are going for the ISO 27001 certification, you will need to determine the scope of your ISMS. The scope can be as specific as a developed application or as broad as the entire security program. Once you determine the scope, then risk management should revolve around risks presented to and around your ISMS.
- When determining the scope of the ISMS, it is also important to identify associated assets along with their criticality.
- Step 2: Identify Risks
- Determine what can happen to cause a potential loss, and to gain insight into how, where and why the loss can happen.
- Include risks that are under the control of your organization.
- Determine applicable threats which has the potential to harm assets applicable to the ISMS.
- Identify existing and planned controls.
- Identify vulnerabilities that can be exploited by threats to cause harm to assets or your organization.
- Identify consequences that losses of confidentiality, integrity and availability may have on assets.
- Step 3: Analyze Risks (Qualitative vs. Quantitative)
- Determine risk analysis approach – either Qualitative or Quantitative.
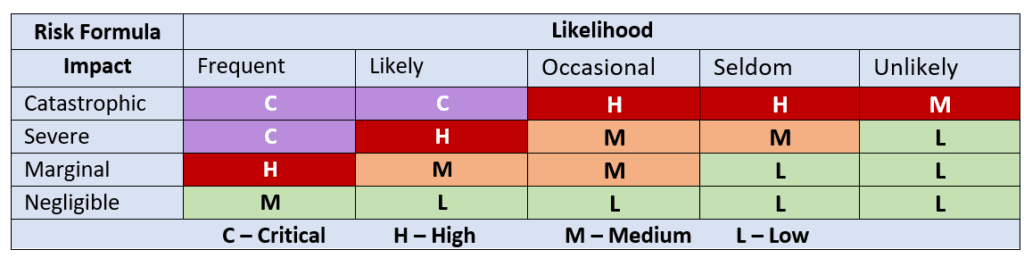
- Qualitative risk analysis uses a scale of qualifying attributes to describe the magnitude of potential consequences (e.g., low, medium, high, and Critical) and the likelihood that those consequences will occur.
- BENEFIT: Simpler to Implement and Highly Subjective
- Qualitative risk analysis uses a scale of qualifying attributes to describe the magnitude of potential consequences (e.g., low, medium, high, and Critical) and the likelihood that those consequences will occur.
- Determine risk analysis approach – either Qualitative or Quantitative.
Qualitative Risk Matrix (Example):
- Quantitative risk analysis uses a scale with numerical values for both consequences and likelihood, using data from a variety of sources.
- BENEFIT: Less subjective, but potentially more accurate depending on the data available for consideration.
Quantitative Risk Matrix (Example):
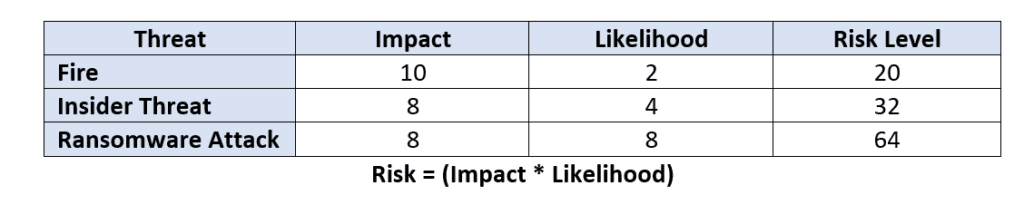
Risk = (Impact * Likelihood)
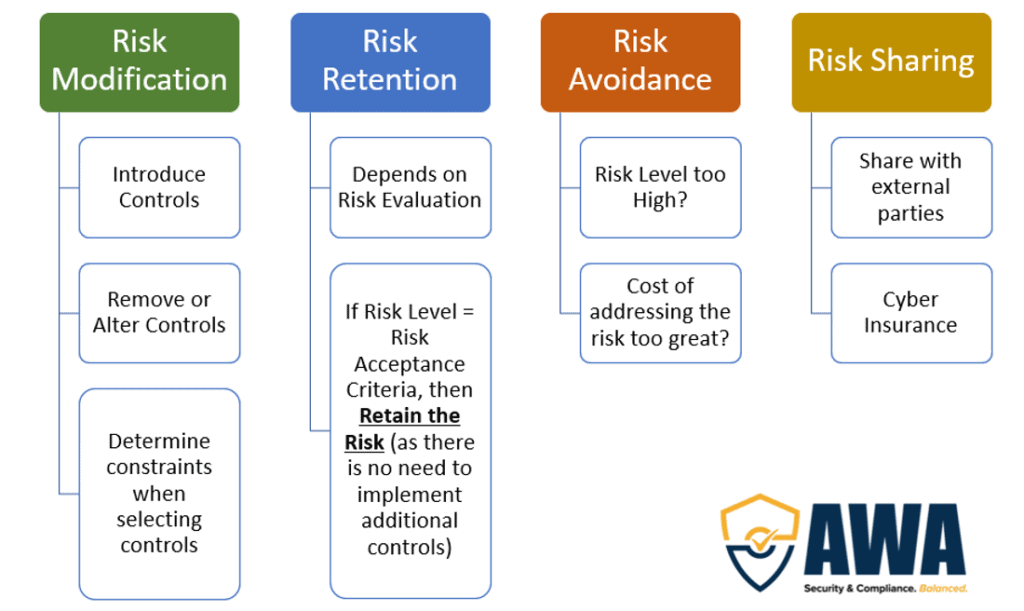
- Step 4: Evaluate Risks
- After you have analyzed/calculated the risk level, you have to evaluate whether they are acceptable or not. If you are following a qualitative approach, then the risk evaluation process is entirely context based. Typically, Low risks are accepted where High and Critical risks are almost always treated.
- If you are following a quantitative approach, then you must determine what the acceptable level of risk is. If the risk is above the acceptable level, then they must be treated further.
- Step 5: Treat Risks
How can AWA Help?
Still unsure where to begin? Let AWA International Group help by performing an ISO-focused Risk Assessment. During the Risk Assessment process, AWA will help achieve the following:
- Advice on the organization’s current cybersecurity risk assessment strategy
- Assist with defining the scope of the ISMS
- Identify appropriate assets associated with the ISMS
- Perform walkthroughs to identify strengths and areas of concern (Risks)
- Recommend remediation activities to treat identified risks
Sources:
ISO/IEC 27001:2013
ISO/IEC 27005:2018
https://advisera.com/27001academy/iso-27001-risk-assessment-treatment-management/







